Secure Web Gateway
Jump toZero Trust web access: The only safe way to browse the web
Go beyond categorizing web access as “safe” or “bad.” Forcepoint ONE SWG enables integration of RBI for secure-container rendering of risky sites, and Zero Trust CDR for complete sanitization of all downloadable documents.
Forcepoint vs. the Competition
Forcepoint
Legacy Security Vendors
(e.g. Zscaler, Netskope)
Legacy Networking Vendors
(e.g. Palo Alto, Fortinet, Check Point)
Secure Web Gateway (SWG) features
- Distributed enforcement
- Public cloud elasticity
- Granular web content filtering
- Mature RBI technology
- RBI file sanitizing with CDR
Data Security Features
- Built-in DLP enforcement
- Extensive predefined policy library
- Classification tagging
- Network enforcement via ICAP

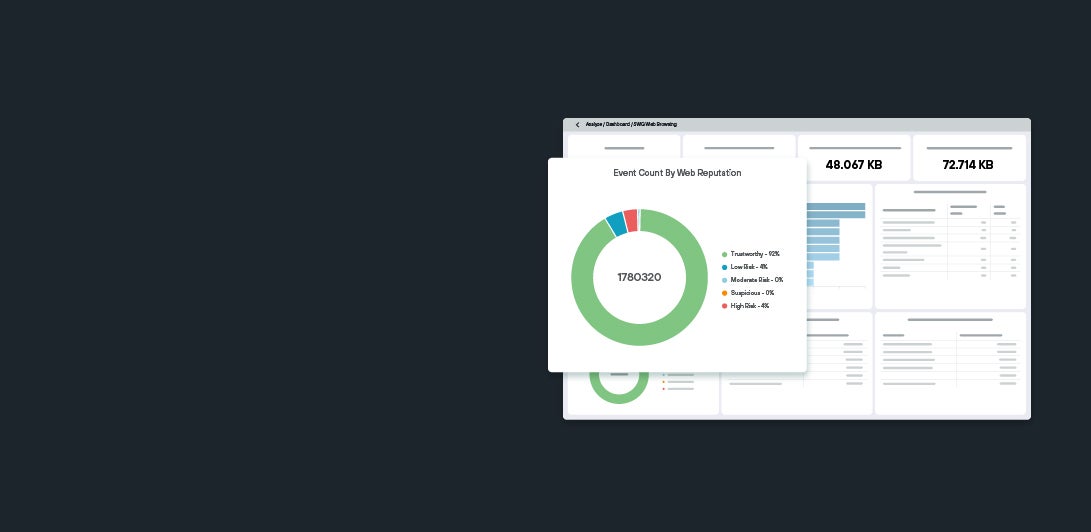
Visualize cloud security return on investment
Calculate the ROI of your investment in cloud security in real-time with an intuitive security analytics dashboard. Centralized visibility simplifies security with telemetry from multiple security services.
Forcepoint ONE SWG is part of the Forcepoint ONE platform

Forcepoint ONE: Forcepoint ONE is a cloud-based, Security Service Edge (SSE) platform. It unifies, simplifies and provides services to enable Zero Trust access and data security, and provides enhanced visibility with security analytics.
Forcepoint ONE CASB: Provide secure access to cloud applications and continuously protect sensitive data in use on any device.
Forcepoint ONE DLP: Prevent data exfiltration on web, cloud and private applications through DLP Software-as-a-Service (SaaS).
Forcepoint ONE ZTNA: Seamlessly extend Zero Trust to private applications in internal data centers and private cloud without the risks or high costs associated with VPNs.
Our Customers
Why Customers Choose Forcepoint ONE SWG

The Forrester Wave™: Security Service Edge Solutions, Q1 2024
Read about Forcepoint ONE and Security Service Edge
Secure Web Gateway (SWG) Resources